Research
|
Research Laboratory
|
Introduction
|
Research Direction
|
|
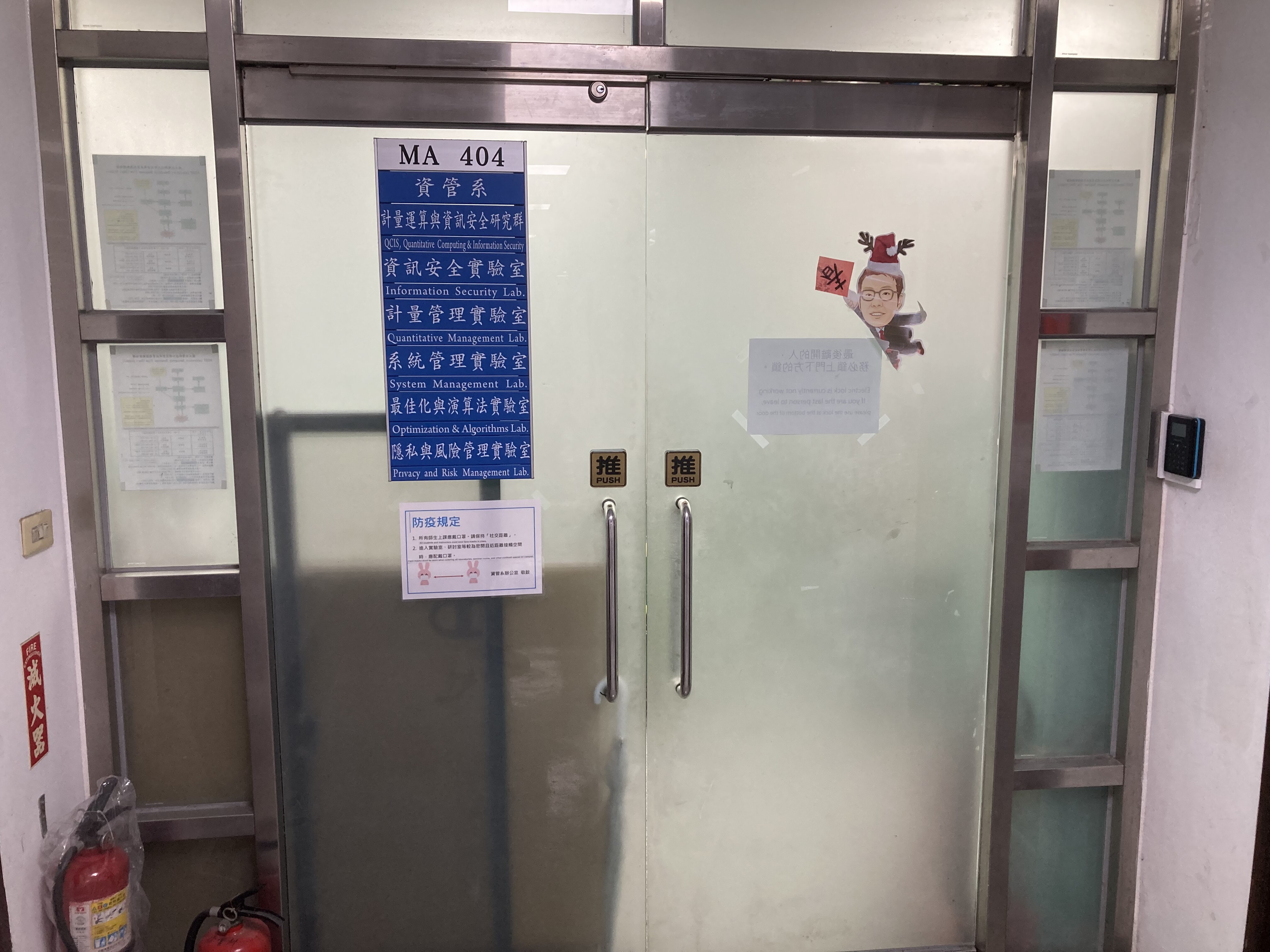
Information Security Laboratory Tel:+ 886-2-2733-3141 ext. 7400 Lab Advisor:Tzong-Chen Wu Scence: |
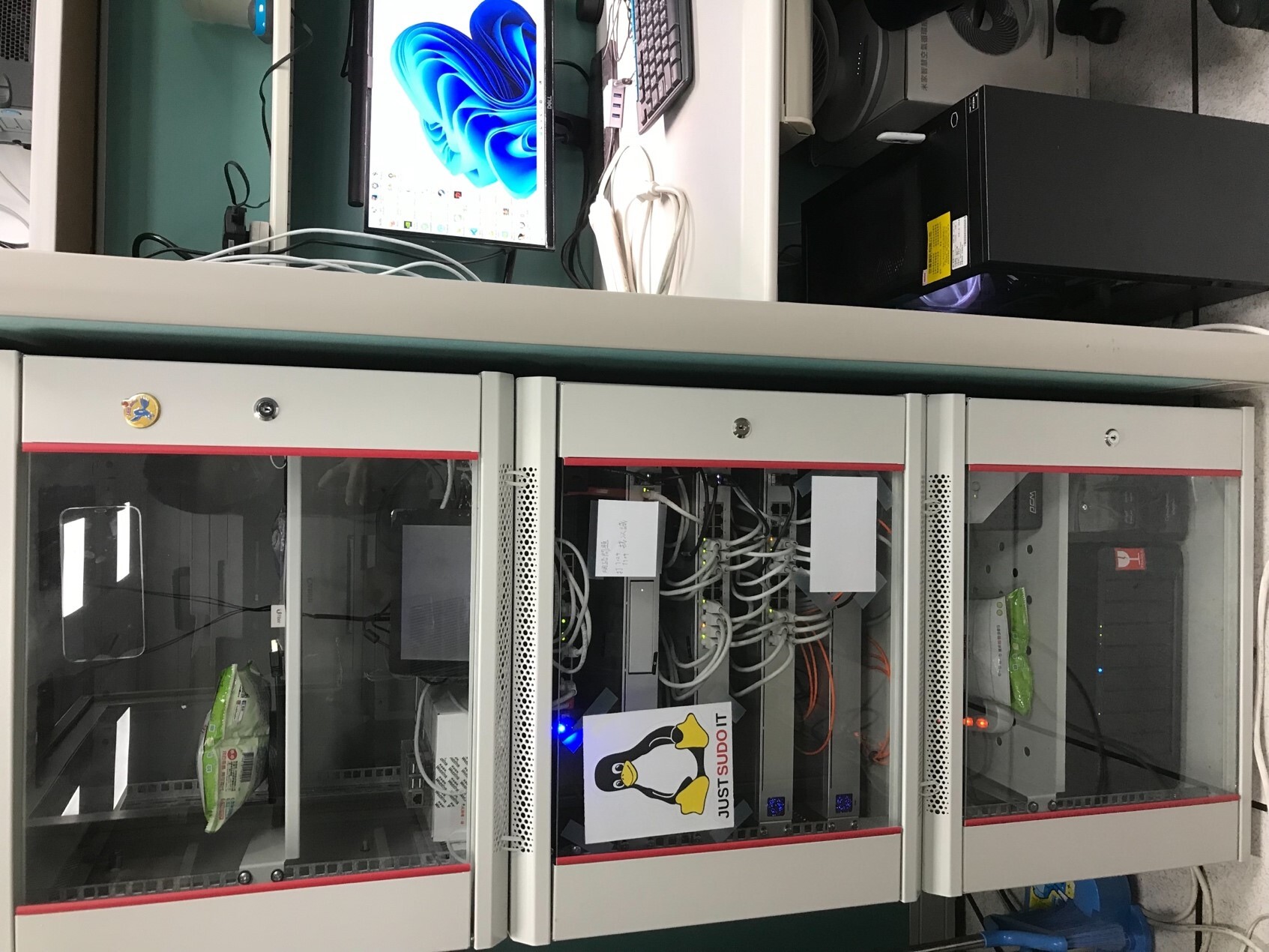
Information Security Laboratory(ISL) is lead by Professor Tzong-Chen Wu since 1992. ISL devotes to the research of information security related issues and collaborative projects with public/private sectors. |
Design and analysis of cryptographic protocols, Security of Internet of Things, Cybersecurity education program |
|
Network Technology and Application Laboratory Tel:+ 886-2-2733-3141 ext. 7904 Lab Advisor:Chiun-Chieh Hsu Scence: |
Since the explosive growth of networks, our laboratory aims at developing new solutions for the network technology and application. |
Our research interests include Data and Text Mining, Wireless Sensor Network, and Parallel and Distributed Processing. |
|
Quantitative Management Laboratory Tel:+ 886-2-2733-3141 ext. 7400 Lab Advisor:Cheng-Kang Chen |
Major Field: Operation Research,Production Management Information System,Decision Support System. |
Major Field: Operation Research,Production Management Information System,Decision Support System. |
|
High-Speed Network Laboratory Tel:+ 886-2-2733-3141 ext. 7905 Lab Advisor:Yuan-Cheng Lai Scence: |
The research area in this laboratory includes all network-related topics. Current research directions mainly focus on AI+5G/6G, AI+Network Security, Quantum Internet, and Performance Analysis. This laboratory is managed by Prof. Yuan-Cheng Lai, who published over 150 journal papers, 130 conference papers, and 30 patents. This laboratory is located in MA301 and has 11 individual spaces for students. Now there are 1 Ph.D. student and 8 master students.
|
AI+5G/6G, AI+Network Security, Quantum Internet, Performance Analysis |
|
Computer Graphics and Multimedia Laboratory Tel:+ 886-2-2733-3141 ext. 7905 Lab Advisor:Chuan-Kai Yang Scence: |
Computer Graphics and Multimedia Laboratory, called CGMLab hereafter, is a laboratory in the department of information management, at National Taiwan University of Science and Technology, led by Prof. Chuan-Kai Yang. Currently there are 6 Phd students, 13 master students, 3 EMBA students, and two groups (with 4 students in each group) of undergrad students. Out of these more than 20 students, about 1/3 are international students, coming from Iran, Vietnam, and Indonesia. As there are so many foreign students, starting from about 5 years ago, all graduate students (except EMBA ones) need to present papers in the weekly group meeting in English. Currently more than 100 research papers, including conference papers and journal papers, have been published, while more than half conference papers are international conference papers, and almost all of journal papers are SCI papers. Prof. Chuan-Kai Yang has got MOST (Ministry of Science and Technology) project funding support every year and has run 15 industrial projects so far. Students with good English and eager to learn how to build multimedia systems are particularly welcome to join CGMLab.
|
The research of CGMLab spans a wide spectrum of multimedia, including image/video/sound processing, computer graphics and scientific/information visualization. In particular, AR/VR and deep learning related topics are being pursued by many students who are seeking new applications of multimedia systems. |
|
Integrated Digital Services Laboratory Tel:+ 886-2-2733-3141 ext. 7904 Lab Advisor:Nai-Wei Lo Scence: |
Integrated Digital Services Laboratory was established in year 2003. The goals of this laboratory are: (2) To educate graduate students to learn how to resolve an open question through doing independent research work, to obtain the capability of writing a formal technical report or academic thesis, and to foster independent thinking. (2) To investigate new technical solutions including infrastructure design and application system design for practical information technology problems and issues such as interoperability, security, performance, efficiency, and reliability. (3) To collaborate with industry companies for developing prototypes, investigating effective solutions or evaluating targeted systems. Regular lab meetings will be scheduled and announced before a new semester starts. In general, a regular lab meeting is held around two hours every week. Graduate students will be assigned to report academic journal/conference papers along with a discussion session within each meeting. |
In recent years, IDSL focuses on new technology development and new system/infrastructure design in information security and privacy protection research areas under various new network environments. Our research directions are depicted in the following: (1) Internet of Vehicles and VANET: trust management in IoV environments, vehicle authentication schemes in IoV or VANET, access control schemes and vehicle traceability schemes in IoV environments, infrastructure design of multi-IoV networks. (2) Blockchain Network and Application: infrastructure design of multi-blockchain networks, federated authentication for multi-blockchain architecture, privacy protection schemes in blockchain networks. (3) Internet of Things including sensors and RFID: firmware update schemes in IoT, object traceability schemes and object identification schemes for RFID-based logistical systems, user authentication on IoT applications. (4) Cloud Computing and Web Services: user authentication for Web services and cloud systems, Single Sign On and access control schemes in Web service architecture, computing resource management schemes in cloud, storage verification or guarantee proof for cloud storage services. (5) Crowdsourcing and Crowdsensing: worker reputation schemes for crowdsensing platforms, infrastructure design of crowdsourcing/crowdsensing frameworks, creditability schemes of sensed data for crowdsourcing/crowdsensing framework.
|
|
Privacy and Risk Manamgement Laboratory Tel:+ 886-2-2733-3141 ext. 7400 Lab Advisor:Shi-Cho Cha Scence: |
Our lab regards the system platform and its application services connected to IoT end devices as where we are coming from, and we develop an end-to-end system security framework based on IoT security technologies. The research of our lab covers the fields of IoT system and network, cryptography, blockchain, cloud environment, security protocol design and analysis, mobile device security mechanism, application service security design, etc. We are dedicated to cultivating the research of system security, network security, cloud security platform, and cryptography theory for participating members. Through the development of prototype systems, we train students to become an information security
|
|
|
Natural User Interface Laboratory Tel:+ 886-2-2733-3141 ext. 7905 Lab Advisor:Bor-Shen Lin Scence:
|
The focus of natural user interface lab is on the technologies for intelligent human-computer interaction with natural language and human knowledge. State-of-the-art artificial intelligence and deep learning algorithms, networks, and frameworks are widely investigated, researched, and developed for emerging applications. | Speech recognition and dialogue, natural language processing, artificial intelligence, deep Learning, knowledge graph, music and multimedia retrieval,. |
|
Labyrinth – Lab, Young & Restless in Threat Hunting Lab Advisor:Raymund Lin |
With a passion for safeguarding digital environments, let us devote to exploring cutting-edge technologies and methodologies to combat cyber threats effectively. |
AI-Assisted Threat Hunting |
|
Optimization and Algorithms Laboratory Tel:+ 886-2-2733-3141 ext. 7400 Lab Advisor:Cheng-Huang Hung Scence: |
Because all the resource are limited, how to use these precious resource more efficiently is an critical and important problem. Operations Research (OR) play the key role to solve these problem. Theories, algorithms, and applications are developed to solve theoretical or real world problems. Even we have more powerful computational ability, we still have to search for faster algorithms and approaches to deal with much more difficult problems and large scale problems. Optimization and Algorithms Lab (OAL) focus on apply Operations Research methodologies, optimization theory and algorithms on the real world problems. Including 1. Develop efficient algorithms or theoretical improvements. 2. Apply existed approach or methodology on the practical side to provide efficient solutions for decision reference. 3. Combine above techniques to establish optimization system or decision support system. The training objectives of Optimization and Algorithms Lab will focus on both theoretical and application sides. The member of OAL will have the following abilities, To understand the optimization theory To construct a model for solving real world problem To design and analyze algorithms To be familiar with existing optimization tools To establish the problem solving ability, including analyzing, modeling, and implementing |
Research Interests Optimization, Operations Research, Algorithms, Network Flow Models, Combinatorial Optimization, and Decision Analysis and Management
Research topics 1. Discrete facility location • Search for stronger IP formulations of discrete facility location problems • Algorithm design • Applications 2. Optimization theory (IP, LP) • Decomposition techniques • Large scale optimization problems 3. Applications of optimization in real world • Transportation and logistics • Supply chain design • Supply chain management 4. Network design • Search for stronger IP formulations of network design problems • Algorithm design • Applications 5. Inverse optimization • Complexity analysis of inverse optimization problems • Formulations of inverse optimization problems • Algorithm design of inverse optimization problems |
|
Applied Cryptology Laboratory Tel:+ 886-2-2733-3141 ext. 7905 Lab Advisor:Jheng-Jia Huang Scence: |
Applied Cryptology Lab, a laboratory that focuses on Information and Communication Security as well as Security Protocol Development and Design | Applied Cryptography, Security Protocol, Information Security Management and Network Security |
|
Software Security Research Laboratory Tel:+ 886-2-2733-3141 ext. Lab Advisor:Ming-Hsien Tsai |
Software bugs in critical systems such as nuclear power plants and cryptographic programs may induce severe damage or security vulnerabilities. It is thus important to assure that correctness of such software implementations. Formal verification is a technique that offers high assurance of software correctness and security. We have developed methods and tools to formally verify cryptographic implementations in industrial libraries such as Bitcoin, BoringSSL,and OpenSSL, as well as post-quantum cryptographic implementations in PQClean and pqm4. We will continue the development of verification methods and tools, and verify more implementations, including but not limited to cryptographic implementations. |
Cryptographic Software Verification, Software Security, Program Analysis, Program Quality Assurance, ω-automata |
|
Network Security Laboratory Tel:+ 886-2-2733-3141 ext. Lab Advisor:Chien-Hua Chiu |
Under Construction. | Under Construction. |
|
Management Information System Laboratory Tel:+ 886-2-2733-3141 ext. 7910 Lab Advisor:Hsi-Peng Lu Scence: |
Established in 1992, MIS Lab focuses on the research on behaviors related to digital transformation in the new economy. For example, the technology acceptance mode, innovation diffusion model, and technology roadmap of various information application systems under 5G, Internet of Things, and AI technology. We also focus on Ubiquinomics under the second-curve perspectives.
|
E-commerce, Digital transformation, and Ubiquinomics |
|
Software Engineering and Management Laboratory Tel:+ 886-2-2733-3141 ext. 7910 Lab Advisor:Sun-Jen Huang |
– Educating students with software engineering and management knowledge – Popularizing the international standards and techniques related to software engineering and management – Promoting the cooperation and interaction between the industry, academic and government – Promoting the competency of the domestic software industry
– Integrating the resources to support the research and education in software engineering and management – Devoting to the theoretical and practical research – Executing cooperation projects with government and industry |
|
|
Information Systems and Innovation Laboratory Tel:+ 886-2-2733-3141 ext. 7916 Lab Advisor:Tzu-Chuan Chou |
Major Field: Information Technology Management,Knowledge Management,Electronic Industry,Electronic Goverment,. |
Major Field: Information Technology Management,Knowledge Management,Electronic Industry,Electronic Goverment,. |
|
Information Systems and Innovation Laboratory Tel:+ 886-2-2733-3141 ext. 7910 Lab Advisor:Yu-Qian Zhu Scence: |
We are a group of curious and fun researchers who explore the interactions between people and information technology. We focus on the management side of technology and investigate the impact of technology on our work and life, as well as how to manage technology to serve the best interest of humanity. | Employees' responses to AI implementation, consumers' adoption of AI technology, IoT privacy, IT in organizations |
|
Electronic Business and Supply Chain Management Laboratory Tel:+ 886-2-2733-3141 ext. 7910 Lab Advisor:Hsiao-Lan Wei Scence: |
Established purpose: In today's business environment where information technology and enterprise operations are inseparable, the business model of enterprises and information technology are seamlessly integrated, and the two merge into one to create a new electronic enterprise model. The cooperation and organizational network among enterprises can bring about the competitive advantage that cannot be produced by individual companies. Therefore, electronic supply chain management has become an important issue for enterprises to create value. |
|